Undergoing a Merger? Hospitals Must Consider These Security Issues
How health IT can remain strong before, during, and after a merger.
In the US healthcare industry, it has become commonplace for hospitals to be involved in mergers and acquisitions. More than 50 hospitals merged in 2017, with the goal of gaining financial benefits and positioning themselves in the rapidly evolving healthcare landscape. However, such mergers create additional complexity to an already complex information technology (IT) landscape.
>>
Complexity is the enemy of security, as the saying goes, and this certainly holds true during hospital mergers and acquisitions. This heightens the risk of security incidents and data breaches for these organizations. Below are 5 M&A security issues to consider during these times of intense change.
1. Information Security Policies
Before the merger or acquisition occurs, the organizations involved must determine how they will align their separate information security policies. The newly merged organization needs to be consistent with its plans to ensure transparency and continuity, not haphazardly use policies from the previously separate entities. The merged company has 3 options moving forward: 1) Pick one group of policies from the previously independent companies and disregard the rest; 2) Write policies from scratch; or 3) Consolidate policies. Once systems are aligned, gaps must be assessed to develop a new information security strategy that enables the hospital to better protect its operations and patients going forward.
2. Identity and Access Management
A crucial question for the newly formed organization is, “How will employee access and user identities be defined?” Oftentimes when a merger occurs, a large influx of users enters the network. Many of these users also become “unknown,” allowing them to perform activities without monitoring and sanctioning, putting your organization at security risk. Users should be identified and given consistent employee access for their role. Some healthcare organizations are using solutions that automate the correlation of detailed user information from human resources and application logs to create accurate and centralized user profiles. This offers enhanced security by providing the clearest picture possible of users and their behaviors within an organization.
When identity is established, the organization should apply the “principle of least privilege,” wherein users are given only the permissions necessary to perform their job.
3. Access by Third Parties
According to a 2017 Ponemon report,
4. Roles and Response
Because 2 or more IT teams are merging, the organization must map out—before an incident occurs—a coordinated incident response to avoid any finger pointing or blame trading. The organization should determine how it integrates monitoring and incident response capabilities and tools. It is essential that the organization respond swiftly and in an methodical manner to information security incidents.
5. Cloud Data
Huge volumes of sensitive data such as electronic protected health information are already scattered across healthcare organizations’ cloud applications and information systems. Merging 2 organizations increases the volume of confidential data and the footprint of that data dispersed over the network. The newly merged organization needs to know where that confidential data exists and how it is being protected. From that assessment, the organization can then standardize its practices to protect that data. Healthcare organizations can use next-generation compliance and information security platforms to protect patient data stored in electronic health records, the cloud, and big data sets, as required by HIPAA.
When healthcare organizations are involved in merger or acquisition activity, the IT security details don’t usually line up neatly. The focus tends to shift away from information security during this time, creating increased risk. Differences among each organization’s procedures, policies, teams, and technologies can lead to gaps in security that cybercriminals are just waiting to exploit. To quickly close these gaps and provide data protection at all times, take a proactive approach to security at each stage of the merger or acquisition. The guidelines above will help steer the course to a successful new organization known for keeping its patient data safe.
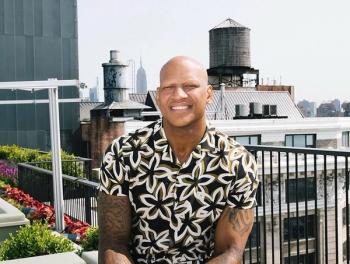
About the Author
Kurt Long is the founder and CEO of FairWarning, a global leader in application security intelligence solutions. FairWarning protects patient information in electronic health records for more than 8500 hospitals and clinics around the world, as well as confidential information in financial services companies with more than $550 billion in assets.
Get the best insights in healthcare analytics
Related